ValorConseilCalvados® offers repair/renovation of Drone Things, Future vision of Smart Drones (IoDT)…
 Support for most brands of drones, Intel-DR®, Parrot®, AR-Drone®, DJI Phantom 2 3 4®, DJI combo S900 S1000®, DJI Inspire 1 2®, DJI MATRICE® M600® M200® M210®, GoPro® Karma®, YUNEEC®, MAVIC® and many more. We have all spare parts at cost via our Taiwanese agency, to have the possibility to produce on demand any need, allowing us to offer you the optimum solution.
Support for most brands of drones, Intel-DR®, Parrot®, AR-Drone®, DJI Phantom 2 3 4®, DJI combo S900 S1000®, DJI Inspire 1 2®, DJI MATRICE® M600® M200® M210®, GoPro® Karma®, YUNEEC®, MAVIC® and many more. We have all spare parts at cost via our Taiwanese agency, to have the possibility to produce on demand any need, allowing us to offer you the optimum solution.
 Drone repair can be handled directly in Caen. You have a doubt… Is the repair of your drone really interesting? Do not hesitate any longer, send us a request for a quote, giving as much information as possible about the breakdown and the model, we will answer you in all transparency, making suggestions adapted to your situation, don’t hesitate to contact us.
Drone repair can be handled directly in Caen. You have a doubt… Is the repair of your drone really interesting? Do not hesitate any longer, send us a request for a quote, giving as much information as possible about the breakdown and the model, we will answer you in all transparency, making suggestions adapted to your situation, don’t hesitate to contact us.
 In the case of a crash linked to a hardware malfunction, after analysis of the logs, we will contact the manufacturer in order to allow us to make the repair free of charge under the cover of our various manufacturer certifications/accreditations (Intel®, DJI®, Flir®, GoPro®, Hubsan®, JJRC®, Parrot®, PowerVision®, SwellPro®, Yuneec®, Zerotech®, iBubble®, Autel® Robotics®, etc.) with the aim of passing your drone under warranty (if this still extends to your product).) with the aim of getting your drone under warranty (if the warranty still applies to your product) so that our technical team is your reference and your sole interlocutor during the entire treatment phase.
In the case of a crash linked to a hardware malfunction, after analysis of the logs, we will contact the manufacturer in order to allow us to make the repair free of charge under the cover of our various manufacturer certifications/accreditations (Intel®, DJI®, Flir®, GoPro®, Hubsan®, JJRC®, Parrot®, PowerVision®, SwellPro®, Yuneec®, Zerotech®, iBubble®, Autel® Robotics®, etc.) with the aim of passing your drone under warranty (if this still extends to your product).) with the aim of getting your drone under warranty (if the warranty still applies to your product) so that our technical team is your reference and your sole interlocutor during the entire treatment phase.
In the event of a crash due to pilot error, our repair service will take charge of your drone in our workshop, allowing a quick intervention, whatever the part to be changed, don‘t hesitate to contact us.
ValorConseilCalvados® offers repair/renovation of Robotic Things, Future vision of Smart Robotic (IoRT)…
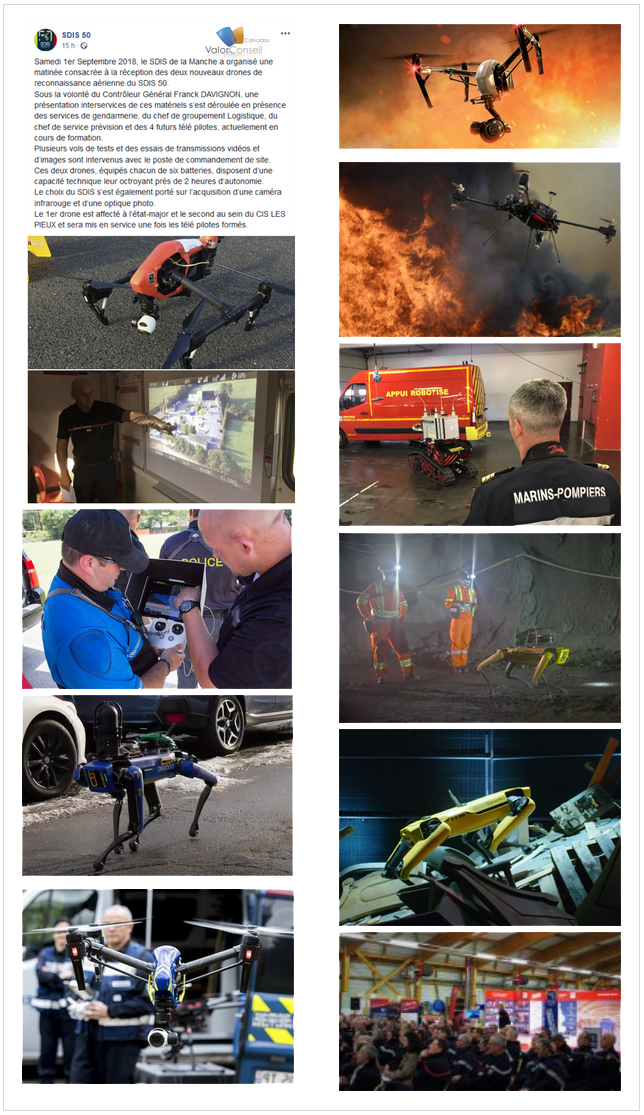
 First use of the word robot in 1921. ValorConseilCalvados® in white label exists since 1954, our first customer in industrial robot installations, in the field of logistics and chemicals, in 1962 was La Chocolaterie-Meunier®, Moulinex®, as well as in the medical, pharmaceutical and food sectors… Our experience of more than half a century is available to you if you wish to have more projection in the approach of your robotics, with solutions capable of adapting to your company reality, don‘t hesitate to contact us.
First use of the word robot in 1921. ValorConseilCalvados® in white label exists since 1954, our first customer in industrial robot installations, in the field of logistics and chemicals, in 1962 was La Chocolaterie-Meunier®, Moulinex®, as well as in the medical, pharmaceutical and food sectors… Our experience of more than half a century is available to you if you wish to have more projection in the approach of your robotics, with solutions capable of adapting to your company reality, don‘t hesitate to contact us.
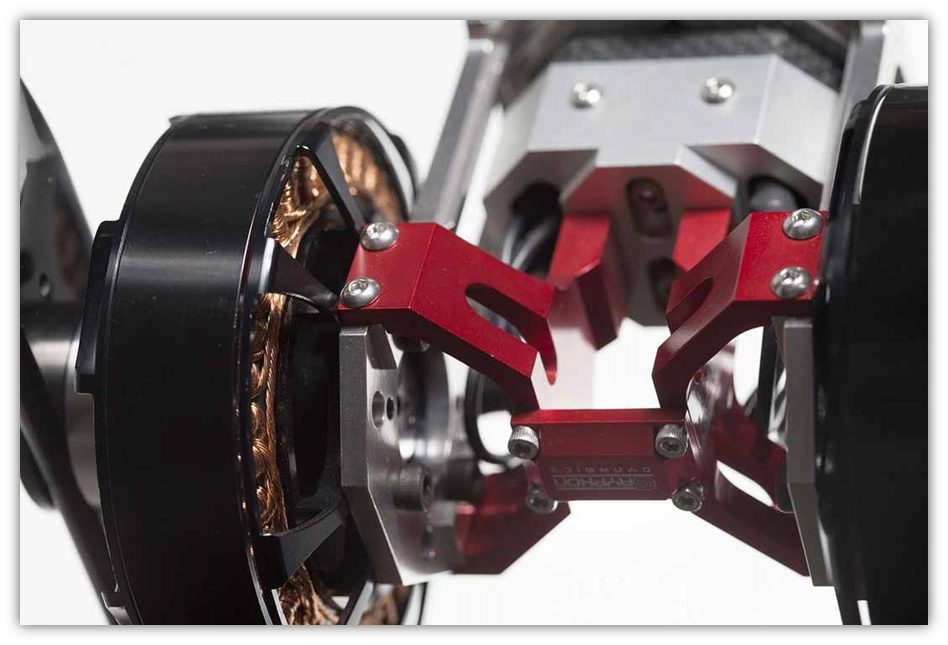
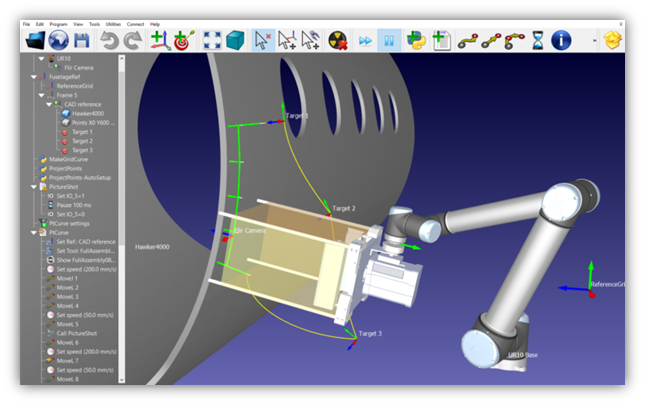
ValorConseilCalvados® Microsoft® Group Partner, part of the TSMC® (Taiwan Semiconductor) Research Center, the Automation and Robotics Group of the Manufacturing Technology Center conducts AI research and development in the area of human-machine interaction, applied to human-robot collaborative tasks in manufacturing and autonomous mobile systems.
Here is a relevant example, for these two areas, it is required to be able to control the applied forces including feedback to the user as well as control the dynamics of the system for stability/performance purposes. ValorConseilCalvados®, owner of several patents, concerning our latest filings in the field of minimization of vibrations and repeated stops, in the field of proximity of possible obstacles using harmonic reduction serving using the force field for the elimination of the elasticity effect.
 Our expertise in the engineering of embedded equipment, such as robotics (IoRT), helps dozens of leading companies and hardware developers to offer new and unique solutions in the industry. If your robot needs to be repaired or upgraded, please send us a request for a quotation with as much information as possible about the problem and the model of the device. We will answer you in all transparency, making suggestions adapted to your situation. As part of our close collaboration with Microsoft®, we have in our team several former engineers of the leaders of the robotics market (IoRT), (Microsoft®, BASF-Robotics®, Canon-Robotics®, BostonDynamics®, ANYbotics® , ExRobotics®, Mitsubishi®, Hitachi-robotics®, UnitreeRobotics®, …). ValorConseilCalvados® offers a wide range of standard and customized maintenance contracts. Our customer service will gladly discuss your application specifications with you to determine a maintenance program that is perfectly adapted to your needs, so please do not don’t hesitate to contact us.
Our expertise in the engineering of embedded equipment, such as robotics (IoRT), helps dozens of leading companies and hardware developers to offer new and unique solutions in the industry. If your robot needs to be repaired or upgraded, please send us a request for a quotation with as much information as possible about the problem and the model of the device. We will answer you in all transparency, making suggestions adapted to your situation. As part of our close collaboration with Microsoft®, we have in our team several former engineers of the leaders of the robotics market (IoRT), (Microsoft®, BASF-Robotics®, Canon-Robotics®, BostonDynamics®, ANYbotics® , ExRobotics®, Mitsubishi®, Hitachi-robotics®, UnitreeRobotics®, …). ValorConseilCalvados® offers a wide range of standard and customized maintenance contracts. Our customer service will gladly discuss your application specifications with you to determine a maintenance program that is perfectly adapted to your needs, so please do not don’t hesitate to contact us.
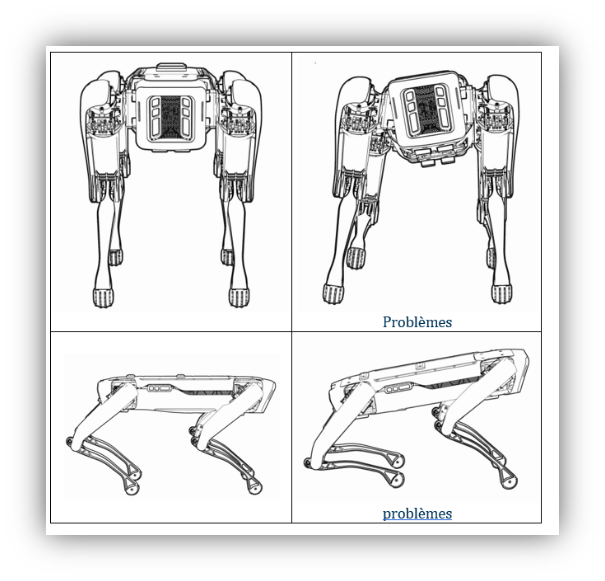 Example of singularity,
Example of singularity,
if you notice any of the following, it may be a sign that camera are not more self-calibrating :
-The robot limps or stumbles more than usual.
-The robot runs into obstacles that it has successfully avoided in the past.
-The robot has more difficulty on the stairs than usual.
Equipped with original manufacturer’s test benches and the skills of manufacturer-trained technicians with knowledge of your products’ every detail, the repair center is your one-stop shop for all repair, standard exchange and upgrade needs. Latest updates, original motors and CNCs, comprehensive functionality tests and CE approved safety tests are part of our expertise.
Our run on the electronic recalibration test bench is used to improve the mobility of the robot with joint and vision calibration. This FPGA recalibration can solve robot gait problems that cannot be solved by traditional self-testing, such as tripping on stairs or limping, by evaluating the current parameters and recalibrating on the FPGAs.
 Dropping the robot and ordinary use over time can cause the robot’s on-board cameras to lose calibration. If the robot starts to run into obstacles that it had previously avoided, you can use the self-test to assess and resolve the camera calibration issues to restore perception accuracy, but if this does not solve your problem we will reprogram the vision FPGA for optimum calibration. After repair :
Dropping the robot and ordinary use over time can cause the robot’s on-board cameras to lose calibration. If the robot starts to run into obstacles that it had previously avoided, you can use the self-test to assess and resolve the camera calibration issues to restore perception accuracy, but if this does not solve your problem we will reprogram the vision FPGA for optimum calibration. After repair :
 -Calibration of joints and camera verification.
-Calibration of joints and camera verification.
-The joint calibration and camera verification mode tests and recalibrates the whole system.
-Load cell sensor for hip and knee joints.
-Joint position sensor for the hip and knee.
Basic verification of all on-board cameras.
-The calculation of new calibrated intrinsic and extrinsic.
 Here is an example of integration, Boston- based equipment Dynamics Robot Spot®, one of our first realizations was a nacelle equipped with a multi-shot launcher of rubber bushes (Flash-ball) with thermal camera and THD camera, 200x zoom, rangefinder and laser tracking (AIFM) for professional use, deterrent, very effective by firing universal caliber rubber cartridges. Sighting, accurate up to 175 meters with a tank of 24 rubber cartridges. Energy 476 joules, kinetic energy: 9.32 joules/cm2, speed: 658 km/h, don’t hesitate to contact us.
Here is an example of integration, Boston- based equipment Dynamics Robot Spot®, one of our first realizations was a nacelle equipped with a multi-shot launcher of rubber bushes (Flash-ball) with thermal camera and THD camera, 200x zoom, rangefinder and laser tracking (AIFM) for professional use, deterrent, very effective by firing universal caliber rubber cartridges. Sighting, accurate up to 175 meters with a tank of 24 rubber cartridges. Energy 476 joules, kinetic energy: 9.32 joules/cm2, speed: 658 km/h, don’t hesitate to contact us.


 We have created a universal gimbal for GoPro® KARMA®. We are constantly improving drone functionality for enterprise applications. We are also finding new ways to jointly develop solutions that open up new applications for drone technology, don’t hesitate to contact us.
We have created a universal gimbal for GoPro® KARMA®. We are constantly improving drone functionality for enterprise applications. We are also finding new ways to jointly develop solutions that open up new applications for drone technology, don’t hesitate to contact us.
 customization, with QLM Technology® the development of a quantum magnetometer solution that detects methane leaks in pipelines up to a distance of 100 meters. The system of measurement weighing a few kg can be embarked in a large-scale drone flying at 50 km/h. They use a laser that illuminates a gaseous medium of variable opacity and a photodetector , don’t hesitate to contact us.
customization, with QLM Technology® the development of a quantum magnetometer solution that detects methane leaks in pipelines up to a distance of 100 meters. The system of measurement weighing a few kg can be embarked in a large-scale drone flying at 50 km/h. They use a laser that illuminates a gaseous medium of variable opacity and a photodetector , don’t hesitate to contact us.


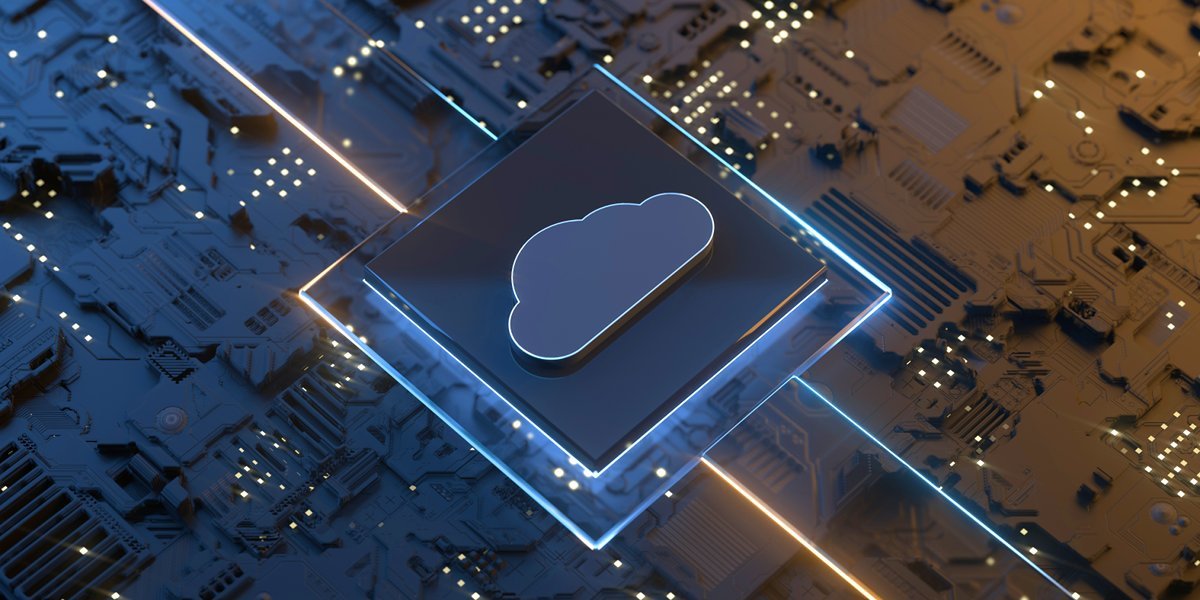
 are ISO9000 certified. ValorConseilCalvados® has been certified as compliant with the ISO/IEC 27001:2013 standard relating to IT security, thanks to our sponsor 9232® de CAEN with the collaborative project 9232® and UMRS® VCCAI23-QZEN®.
are ISO9000 certified. ValorConseilCalvados® has been certified as compliant with the ISO/IEC 27001:2013 standard relating to IT security, thanks to our sponsor 9232® de CAEN with the collaborative project 9232® and UMRS® VCCAI23-QZEN®. Cybersecurity is no longer a human-scale problem. Organizations need to adopt AI-based protections that can defend against increasingly automated attacks. In an era where cyberattacks are evolving rapidly and threat actors strike deliberately when security teams are out of the office, artificial intelligence technologies have become essential for taking targeted action to contain attacks without disrupting business. normal.
Cybersecurity is no longer a human-scale problem. Organizations need to adopt AI-based protections that can defend against increasingly automated attacks. In an era where cyberattacks are evolving rapidly and threat actors strike deliberately when security teams are out of the office, artificial intelligence technologies have become essential for taking targeted action to contain attacks without disrupting business. normal. Since its launch in 2000, ValorConseilCalvados® has joined the national victim assistance system “Cybermalveillance.gouv.fr” as a service provider referenced on the platform and has joined the Cybersecurity and Infrastructure Security Agency CISA system “cisa.gov /uscert”. It was launched on October 17, 2017. As provided for in the service providers’ commitment charter, we will send our intervention reports, technical elements and all useful information that will allow us to fight against cyber-maliciousness. Cybermalveillance.gouv.fr is present on the social networks Twitter and Facebook. If you have accounts on these networks, we invite you to subscribe in order to follow the news that will be published there.
Since its launch in 2000, ValorConseilCalvados® has joined the national victim assistance system “Cybermalveillance.gouv.fr” as a service provider referenced on the platform and has joined the Cybersecurity and Infrastructure Security Agency CISA system “cisa.gov /uscert”. It was launched on October 17, 2017. As provided for in the service providers’ commitment charter, we will send our intervention reports, technical elements and all useful information that will allow us to fight against cyber-maliciousness. Cybermalveillance.gouv.fr is present on the social networks Twitter and Facebook. If you have accounts on these networks, we invite you to subscribe in order to follow the news that will be published there. ValorConseilCalvados® cyber forensic analysts are highly skilled in identifying, isolating and unraveling complex data networks associated with domains, websites and hosting accounts. Our team connects digital leads to people, corporations, business partners. Due to the nature of the Internet, our team can investigate websites hosted anywhere in the world and for clients in any country. The team has extensive experience applying its capabilities in support of various types of investigations, including cyber fraud, scams, copyright and defamation. Due to the constant evolution of the Internet and criminal techniques, our team makes sure to keep abreast of the changes and in many ways are at the forefront of the art of website cybercrime.
ValorConseilCalvados® cyber forensic analysts are highly skilled in identifying, isolating and unraveling complex data networks associated with domains, websites and hosting accounts. Our team connects digital leads to people, corporations, business partners. Due to the nature of the Internet, our team can investigate websites hosted anywhere in the world and for clients in any country. The team has extensive experience applying its capabilities in support of various types of investigations, including cyber fraud, scams, copyright and defamation. Due to the constant evolution of the Internet and criminal techniques, our team makes sure to keep abreast of the changes and in many ways are at the forefront of the art of website cybercrime. Our investigators and intelligence specialists come from private backgrounds and governmental. Although police departments have the experience, capacity and access to limited source information, they are simply overwhelmed by the sheer number of reports to provide you with the service you deserve. In fact, many police departments around the world actively refer victims to private investigators because they admit that the police do not have the resources available to meet the demand. However, this scenario can be beneficial for victims. In the case of investigations, we do not have the same time frame to launch your investigation and can quickly identify and capture evidence through our extensive international network. Once the evidence and information is gathered for your case, it can be referred to the police who are likely to be more enthusiastic. We have extensive experience with various police departments and understand their investigative evidence requirements and processes. Investigators are engaged in full-time online (cyber) investigations and we are proud to be pioneers in the international industry. For more information about our online survey services, please contact us for a free consultation and confidential review of your needs.
Our investigators and intelligence specialists come from private backgrounds and governmental. Although police departments have the experience, capacity and access to limited source information, they are simply overwhelmed by the sheer number of reports to provide you with the service you deserve. In fact, many police departments around the world actively refer victims to private investigators because they admit that the police do not have the resources available to meet the demand. However, this scenario can be beneficial for victims. In the case of investigations, we do not have the same time frame to launch your investigation and can quickly identify and capture evidence through our extensive international network. Once the evidence and information is gathered for your case, it can be referred to the police who are likely to be more enthusiastic. We have extensive experience with various police departments and understand their investigative evidence requirements and processes. Investigators are engaged in full-time online (cyber) investigations and we are proud to be pioneers in the international industry. For more information about our online survey services, please contact us for a free consultation and confidential review of your needs.
 The operation of unmanned aircraft is covered by Implementing Regulation (EU) 947 on rules and procedures for the operation of unmanned aircraft. This regulation describes in particular the requirements associated with this operation around the following themes:
The operation of unmanned aircraft is covered by Implementing Regulation (EU) 947 on rules and procedures for the operation of unmanned aircraft. This regulation describes in particular the requirements associated with this operation around the following themes:

 Support for most brands of drones, Intel-DR®, Parrot®, AR-Drone®, DJI Phantom 2 3 4®, DJI combo S900 S1000®, DJI Inspire 1 2®, DJI MATRICE® M600® M200® M210®, GoPro® Karma®, YUNEEC®, MAVIC® and many more. We have all spare parts at cost via our Taiwanese agency, to have the possibility to produce on demand any need, allowing us to offer you the optimum solution.
Support for most brands of drones, Intel-DR®, Parrot®, AR-Drone®, DJI Phantom 2 3 4®, DJI combo S900 S1000®, DJI Inspire 1 2®, DJI MATRICE® M600® M200® M210®, GoPro® Karma®, YUNEEC®, MAVIC® and many more. We have all spare parts at cost via our Taiwanese agency, to have the possibility to produce on demand any need, allowing us to offer you the optimum solution.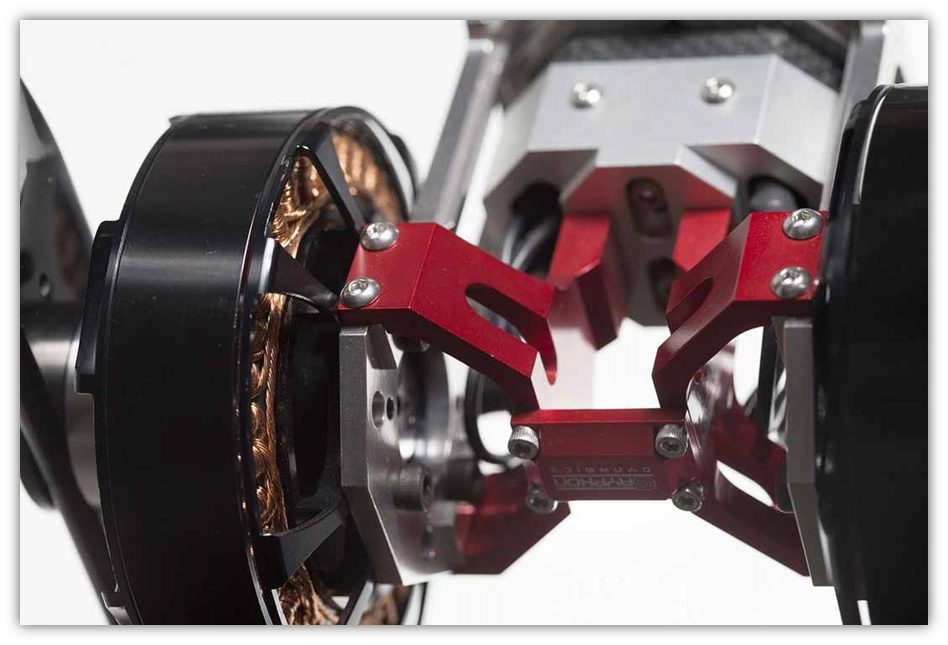 Drone repair can be handled directly in Caen. You have a doubt… Is the repair of your drone really interesting? Do not hesitate any longer, send us a request for a quote, giving as much information as possible about the breakdown and the model, we will answer you in all transparency, making suggestions adapted to your situation,
Drone repair can be handled directly in Caen. You have a doubt… Is the repair of your drone really interesting? Do not hesitate any longer, send us a request for a quote, giving as much information as possible about the breakdown and the model, we will answer you in all transparency, making suggestions adapted to your situation, In the case of a crash linked to a hardware malfunction, after analysis of the logs, we will contact the manufacturer in order to allow us to make the repair free of charge under the cover of our various manufacturer certifications/accreditations (Intel®, DJI®, Flir®, GoPro®, Hubsan®, JJRC®, Parrot®, PowerVision®, SwellPro®, Yuneec®, Zerotech®, iBubble®, Autel® Robotics®, etc.) with the aim of passing your drone under warranty (if this still extends to your product).) with the aim of getting your drone under warranty (if the warranty still applies to your product) so that our technical team is your reference and your sole interlocutor during the entire treatment phase.
In the case of a crash linked to a hardware malfunction, after analysis of the logs, we will contact the manufacturer in order to allow us to make the repair free of charge under the cover of our various manufacturer certifications/accreditations (Intel®, DJI®, Flir®, GoPro®, Hubsan®, JJRC®, Parrot®, PowerVision®, SwellPro®, Yuneec®, Zerotech®, iBubble®, Autel® Robotics®, etc.) with the aim of passing your drone under warranty (if this still extends to your product).) with the aim of getting your drone under warranty (if the warranty still applies to your product) so that our technical team is your reference and your sole interlocutor during the entire treatment phase. First use of the word robot in 1921. ValorConseilCalvados® in white label exists since 1954, our first customer in industrial robot installations, in the field of logistics and chemicals, in 1962 was La Chocolaterie-Meunier®, Moulinex®, as well as in the medical, pharmaceutical and food sectors… Our experience of more than half a century is available to you if you wish to have more projection in the approach of your robotics, with solutions capable of adapting to your company reality,
First use of the word robot in 1921. ValorConseilCalvados® in white label exists since 1954, our first customer in industrial robot installations, in the field of logistics and chemicals, in 1962 was La Chocolaterie-Meunier®, Moulinex®, as well as in the medical, pharmaceutical and food sectors… Our experience of more than half a century is available to you if you wish to have more projection in the approach of your robotics, with solutions capable of adapting to your company reality, Our expertise in the engineering of embedded equipment, such as robotics (IoRT), helps dozens of leading companies and hardware developers to offer new and unique solutions in the industry. If your robot needs to be repaired or upgraded, please send us a request for a quotation with as much information as possible about the problem and the model of the device. We will answer you in all transparency, making suggestions adapted to your situation. As part of our close collaboration with Microsoft®, we have in our team several former engineers of the leaders of the robotics market (IoRT), (Microsoft®, BASF-Robotics®, Canon-Robotics®, BostonDynamics®, ANYbotics® , ExRobotics®, Mitsubishi®, Hitachi-robotics®, UnitreeRobotics®, …). ValorConseilCalvados® offers a wide range of standard and customized maintenance contracts. Our customer service will gladly discuss your application specifications with you to determine a maintenance program that is perfectly adapted to your needs, so please do not
Our expertise in the engineering of embedded equipment, such as robotics (IoRT), helps dozens of leading companies and hardware developers to offer new and unique solutions in the industry. If your robot needs to be repaired or upgraded, please send us a request for a quotation with as much information as possible about the problem and the model of the device. We will answer you in all transparency, making suggestions adapted to your situation. As part of our close collaboration with Microsoft®, we have in our team several former engineers of the leaders of the robotics market (IoRT), (Microsoft®, BASF-Robotics®, Canon-Robotics®, BostonDynamics®, ANYbotics® , ExRobotics®, Mitsubishi®, Hitachi-robotics®, UnitreeRobotics®, …). ValorConseilCalvados® offers a wide range of standard and customized maintenance contracts. Our customer service will gladly discuss your application specifications with you to determine a maintenance program that is perfectly adapted to your needs, so please do not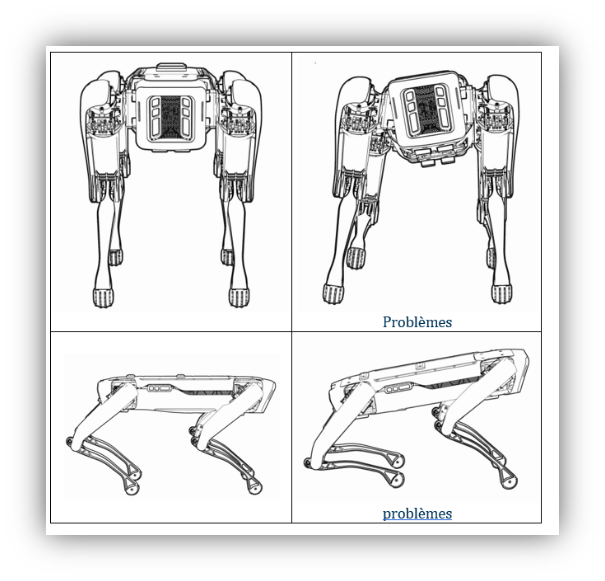 Example of singularity,
Example of singularity, 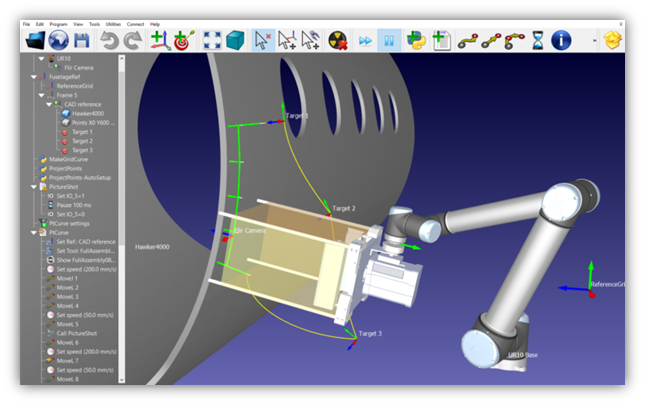 Dropping the robot and ordinary use over time can cause the robot’s on-board cameras to lose calibration. If the robot starts to run into obstacles that it had previously avoided, you can use the self-test to assess and resolve the camera calibration issues to restore perception accuracy, but if this does not solve your problem we will reprogram the vision FPGA for optimum calibration. After repair :
Dropping the robot and ordinary use over time can cause the robot’s on-board cameras to lose calibration. If the robot starts to run into obstacles that it had previously avoided, you can use the self-test to assess and resolve the camera calibration issues to restore perception accuracy, but if this does not solve your problem we will reprogram the vision FPGA for optimum calibration. After repair : -Calibration of joints and camera verification.
-Calibration of joints and camera verification. Here is an example of integration,
Here is an example of integration,

 This is the standard treatment suitable for: corrosive environments with oil
This is the standard treatment suitable for: corrosive environments with oil  and solvent splashes, climates at all latitudes with relative humidity up to 98% at a temperature of -80 to 140°C, without large variations in these which can cause strong condensation or even water run-off.
and solvent splashes, climates at all latitudes with relative humidity up to 98% at a temperature of -80 to 140°C, without large variations in these which can cause strong condensation or even water run-off.